A reader sent me the link for a new software protection package called Software Passport (here). This is from The Silicons Realms, the makers of Armadillo for Windows. Since I’m as curious as a cat, I started giving a quick look on it, to see if it has any interesting things related to anti-debugging and anti-disassembly.
The good news is that there are some new tricks that I haven’t seen before, for example, GDB can’t trace the initial loader. I haven’t explored this yet so I don’t know how it’s being done. When I approach a target, I prefer to understand the general pattern of things instead going immediatly to understand every single obstacle that appears.
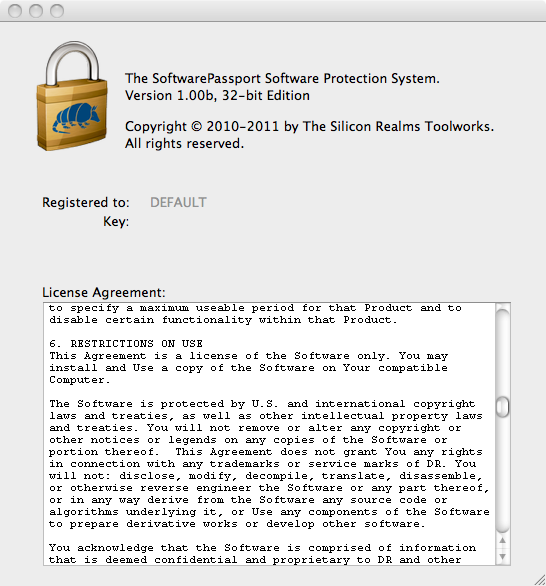
The bad news is that the packed/encrypted/whatever binary is easy to dump and recover, allowing to disassemble and poking at the real binary. I was interested in finding the registration routine (I’m playing with the protector itself) but it’s not so straightforward. Anyway, the following screenshot shows that’s easy to dump the binary and modify things. It’s still too early and too much left to explore but I have a feeling that this protection needs more work 😉.
Have fun,
fG!